The cybersecurity market was valued at about $197 billion in 2020 and is projected to rise to $478+ billion in the next eight years. As the space continues to grow, both startups and legacy cybersecurity vendors are aware of the sheer number of vendors and must consider how they can better work together to help enterprises solve cybersecurity challenges.
Two of the biggest challenges? The first is that CISOs (Chief Information Security Officers), CIOs, and their teams are juggling too many security products and services. In the unfortunate event of a breach, they must juggle numerous pieces of software to create reports and review all possible indicators of compromise, all of which impacts dwell and response times and ultimately gives bad actors more time to steal data and cause serious damage. The second challenge is that limited budgets and resources are further straining IT teams, forcing them to find more value from their solutions.
For CISOs and their teams to be successful, they cannot rely on a growing list of security products to function. While it is true that many of these solutions are essential and address the unique issues enterprises face today, the volume of technologies CISOs and their teams must navigate is making it difficult to adequately respond to new and emerging threats.
Vendor consolidation for CISOs is top priority, and a Gartner survey found that 80 percent of respondents are planning for a vendor consolidation strategy in the next three years, and 30 percent are already in the process of consolidating. While consolidating every security product and service is not possible, building a cybersecurity tech stack with open and interoperable solutions is very realistic. To truly solve cybersecurity threats and help practitioners, identity and cybersecurity solutions need to break down existing silos and interoperate.
An Open and Interoperable Cybersecurity Future
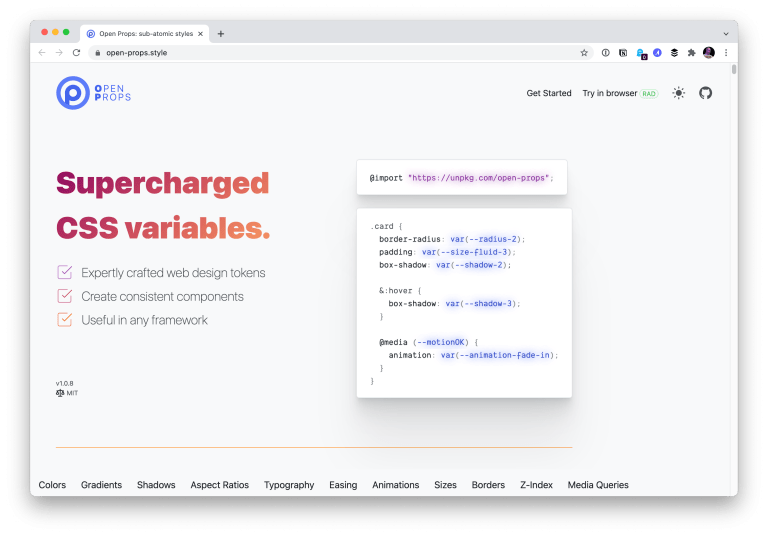
The concept of openness and interoperability as it relates to cybersecurity means solutions integrate with common enterprise applications and services by leveraging common industry standards (aka OpenID Connect, SAML, and FIDO in the authentication space and open APIs for various other offerings). This ensures external developers can access the software they need.
This concept was first made popular in Gartner’s Cybersecurity Mesh Architecture. Cybersecurity vendors must fully embrace this concept to enable orchestration and automation for CISOs and their organizations to best meet modern business demands.
All segments within the cybersecurity market can greatly benefit from the concept of openness and interoperability. One such segment is the PKI (public key infrastructure), Certificate Authority (CA), and digital certificate space. Today, the world’s data is secured with technology that acts like a passport. This technology – a PKI digital certificate issued by a CA – contains identity information related to the holder. In the digital world, certificates act as passports for humans and the machines and applications they use (i.e. devices, software, code, bots, IoT/OT, etc.). These cryptographic certificates are proven in their ability to establish digital trust.
With the rapid shift to remote work, a company’s data is no longer behind a firewall but rather being accessed from locations around the world. Therefore, the data is likely to cross hostile network boundaries. The digital identity of humans and machines is the new perimeter, which is why there’s been a dramatic increase in demand for certificates. The mounting challenge for enterprises now is governing these certificates, which can be issued by any number of CAs.
According to a Sectigo survey, 59 percent of enterprises have deployed digital certificates from multiple CAs. This is a prime example of IT teams engaging with overlapping solutions to secure their networks. Without open and interoperable security solutions, these teams must invest in multiple Certificate Lifecycle Management (CLM) solutions or consolidate their certificates under one CA – neither option is realistic. The same survey revealed that 80 percent of enterprise leaders believe it’s important for their CLM solution to support management through a single pane of glass.
Next-generation Certificate Lifecycle Management
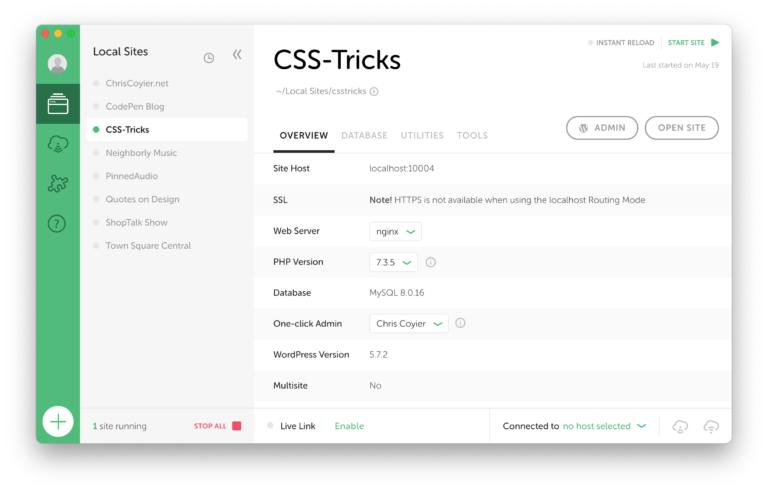
For a CLM solution to meet these needs of enterprise IT leaders today, it must work with a host of different IT environments, including digital certificate types and use cases, and certificate origins. CLM needs to be CA agnostic with the power to discover, govern, and manage the lifecycle of any certificate, regardless of what CA it came from.
As IT teams continue to enhance and grow their cybersecurity infrastructures, they face a widening security perimeter that can see millions of endpoints and siloed certificate and identity management. It is critical to have a universal, high-value solution with the power to automate every single certificate’s lifecycle. This is the only way enterprises can effectively manage their digital identities at scale.
The modern approach to CLM is a CA agnostic cloud-first solution that delivers a single administration portal to secure and manage growing numbers of digital identities, both human and machine. Further than just managing digital certificates, the CLM solution must also focus on enabling use cases that support business outcomes, such as secure email and DevOps security. The goal must be to ease security, complexity, management, and orchestration for IT leaders. This must be enabled at a foundational level, with a focus on openness and interoperability with leading technology stacks.
No longer can IT teams slap on band-aids and duct tape solutions just to keep things moving along. All digital businesses need a firm foundation of digital trust and identity-first security to compete and operate today, and this must start with flexible, cloud-first, digital identities, enabled with a digital certificate platform that is CA agnostic and includes CLM functionality. Of course, that is in addition to other identity security tools, technologies, and processes.
Establishing digital trust is no longer a ‘nice to have.’ Enterprises across the globe need to invest in CLM that leverages open standards and can easily interoperate with existing technology solutions. This will only be possible if the cybersecurity industry adopts an open and interoperable approach to developing products.